What Is Change Management in IT Operations?
Change is unavoidable in IT operations, providing a clear, risk-based framework to introduce improvements while protecting service stability.
What is Change Management?
Change Management in IT is a structured practice within IT Service Management (ITSM) that governs how modifications to systems, infrastructure, and services are introduced. It defines how changes are requested, assessed, approved, prioritized, scheduled, and implemented.
In ITIL 4, the term has evolved into change enablement. This shift in language reflects an important insight: the purpose of the practice is not to prevent change, but to enable it safely.
A change, in this context, is any addition, modification, or removal that could directly or indirectly affect IT services. That includes deploying a new application, upgrading a server, adjusting firewall rules, migrating data, or retiring legacy hardware.
What Change Management provides is a controlled path between intention and execution. Without it, even minor technical adjustments can trigger outages, security gaps, compliance violations, or operational instability.
IT Change Management vs. Organizational Change Management
The phrase “change management” is often used broadly, which leads to confusion. In many organizations, it refers to managing people’s reactions to transformation: communication plans, training programs, and adoption strategies. That is Organizational Change Management.
IT Change Management is different. It focuses specifically on technical changes to systems and infrastructure. Its primary objective is operational stability: minimizing disruption, reducing risk, and ensuring that services continue to function as expected.
Organizational Change Management, on the other hand, addresses the human dimension. It ensures that employees understand and adopt new tools or processes.
For example, if a company introduces a new service desk platform:
- **IT Change Management **ensures the system is deployed correctly and without disrupting existing services.
- **Organizational Change Management **ensures that employees know how to use it effectively.
The Role of Change Management in ITIL
Within the ITIL framework, Change Management has long been a core practice. In earlier ITIL versions, Change and Release Management were part of the Service Transition lifecycle stage.
Within ITIL 4’s Service Value System (SVS), Change Enablement supports value creation by ensuring that improvements and modifications do not undermine service stability.
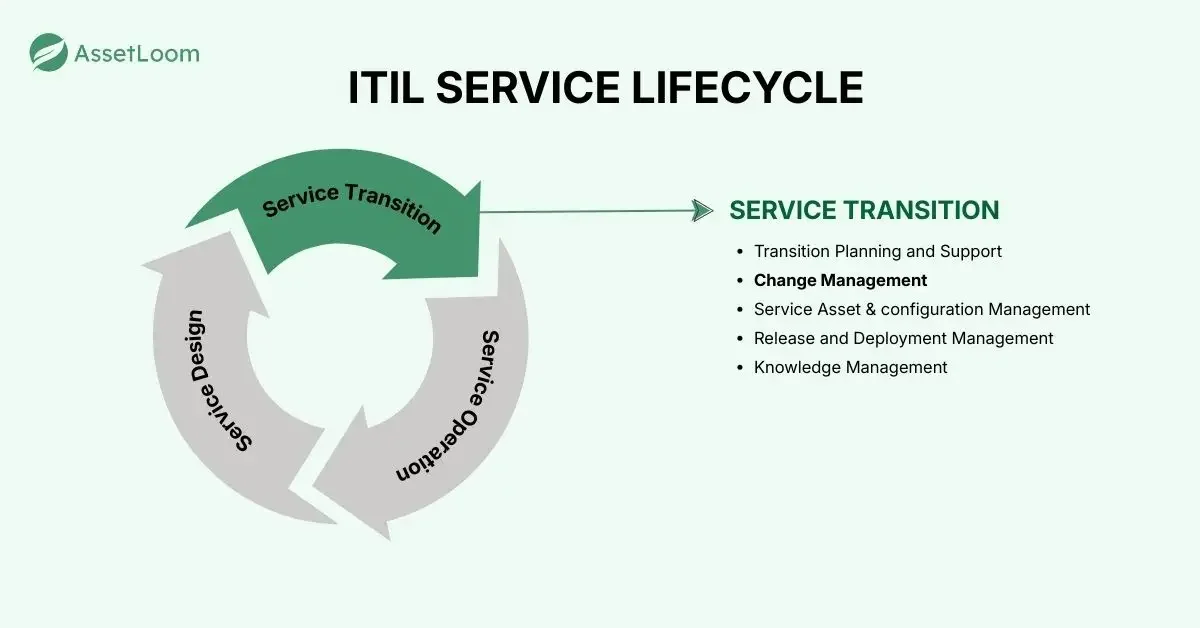
It connects closely with practices such as:
- Incident Management
- Problem Management
- Release Management
- Risk Management
For example:
- If repeated incidents trace back to unauthorized system modifications, the issue is often weak change control.
- If deployments repeatedly fail, it may indicate gaps in risk assessment or approval workflows.
In this way, Change Management acts as a stabilizing mechanism within the broader service management ecosystem.
Types of Changes
One of the most practical insights in ITIL is the classification of changes into three categories: standard, normal, and emergency.
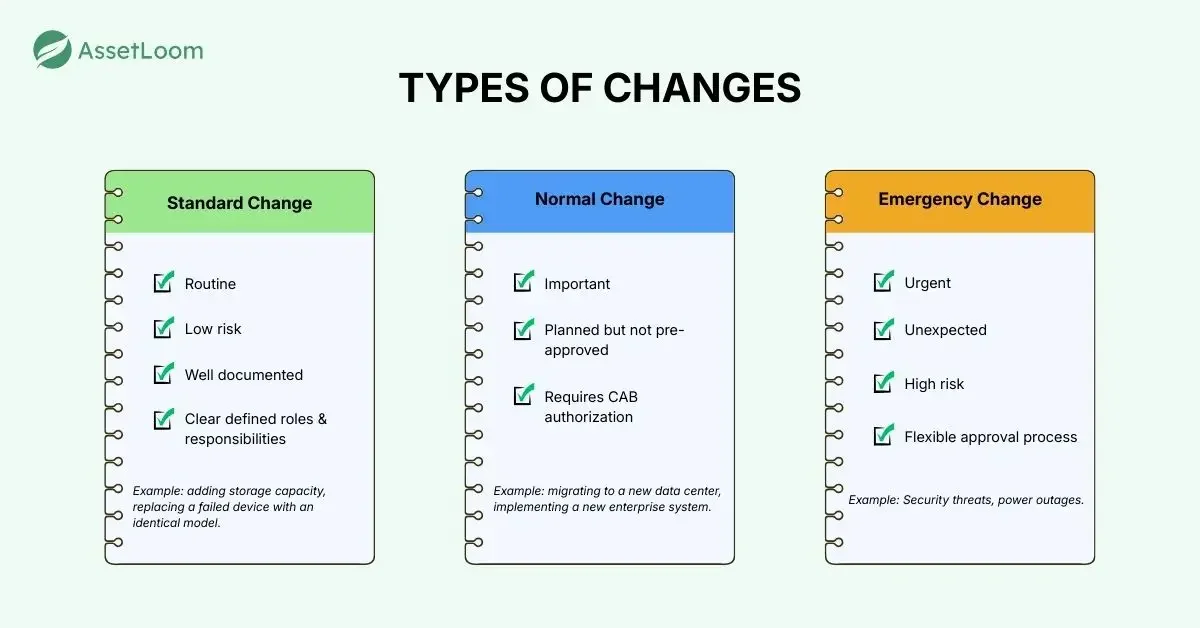
Standard changes
Standard changes are routine, low-risk, and pre-approved. They follow a documented process and have already undergone risk assessment. Examples include adding storage capacity, replacing a failed device with an identical model, or provisioning a predefined database instance. Because these changes are predictable, they are often strong candidates for automation.
Normal changes
Normal changes are planned but not pre-approved. They require assessment, authorization, and scheduling. Examples include migrating to a new data center, implementing a new enterprise system, or introducing significant performance upgrades. Some normal changes may require review by a Change Advisory Board (CAB), particularly if they carry substantial risk.
Emergency changes
Emergency changes arise from unexpected incidents or security threats. They must be implemented quickly to restore service or protect systems. Applying a critical security patch or resolving a major outage are typical examples. In these cases, the urgency of action outweighs the risk of delay.
What IT Change Management Process Looks Like in Practice
Although ITIL does not prescribe a rigid workflow, most Change Management processes follow a logical sequence.
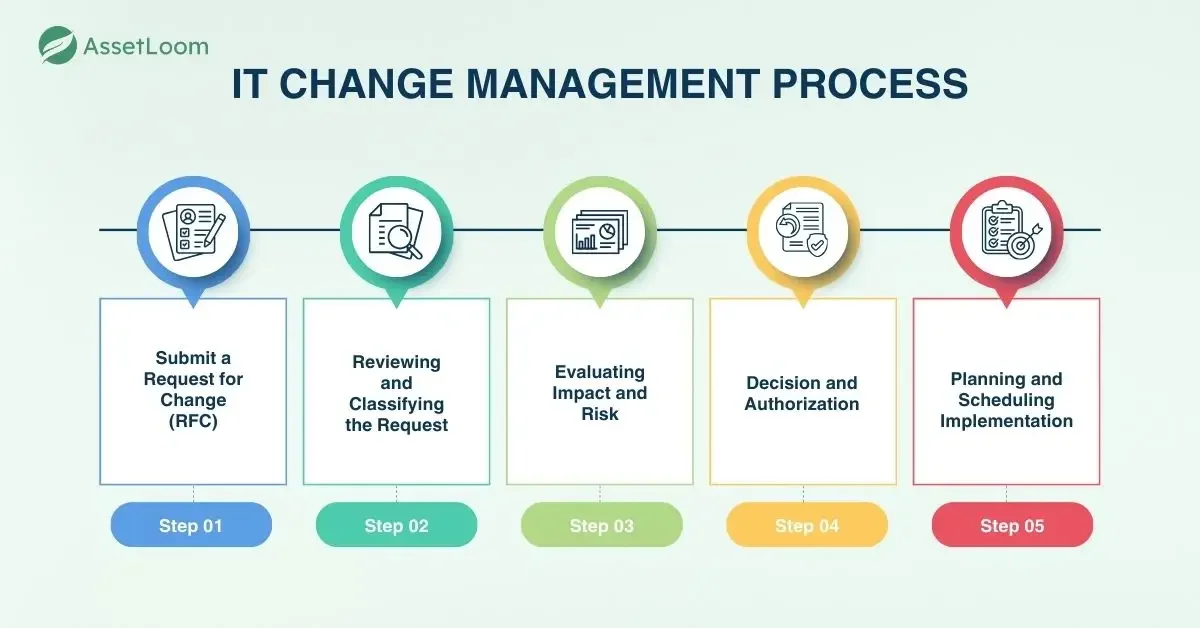
1. Submit a Request for Change (RFC)
It begins with a formal Request for Change (RFC). The change requester documents the nature of the change. The depth of detail typically depends on the type and impact of the change.
An RFC typically includes:
- Description of the change
- Business reason
- Systems affected
- Risk assessment
- Rollback plan
When a Request for Change (RFC) is submitted, teams need to clearly identify which assets are involved (e.g., servers, applications, network devices, or software licenses).
If asset records are incomplete or outdated, the impact assessment becomes unreliable. Missing dependencies can lead to service disruptions, compliance violations, or unexpected downtime. Accurate IT asset data ensures that changes are evaluated with full visibility into what is actually being modified.
Explore Top 10 Automated Asset Management Tool - 2026 Updated
2. Reviewing and Classifying the Request
Once submitted, the RFC is examined by the person responsible for overseeing the Change Management process. This role is often referred to as the Change Manager or change owner.
At this stage, the request is reviewed to ensure it is complete and clearly defined. It is then categorized (for example, as standard, normal, or emergency) and assigned a priority level.
Based on this evaluation, the change may move forward for deeper assessment, be declined, or be returned to the requester for clarification or additional information.
3. Evaluating Impact and Risk
After the initial review, the proposed change undergoes a more detailed analysis. The objective here is to understand how the change might affect systems, services, and the broader business environment.
This evaluation includes identifying potential risks, service disruptions, dependencies, and failure scenarios. Financial implications, compliance requirements, and regulatory constraints should also be considered.
For higher-risk or more complex changes, a Change Advisory Board (CAB) may be consulted to provide expert input and balanced recommendations.
4. Decision and Authorization
Once the impact and risk assessment is complete, the change is presented to the appropriate decision-makers. These authorities determine whether the change should proceed, be modified, or be rejected.
Approval levels typically depend on the nature and risk level of the change. Approvers often ask:
- Is this hardware still under support?
- Will this change violate license terms?
- Is there budget allocated for replacement?
- Does this device fall under regulatory control?
These questions are answered through IT Asset Management data. Change decisions are only as strong as the asset intelligence behind them.
5. Planning and Scheduling Implementation
After approval is granted, attention shifts to execution planning. Relevant stakeholders collaborate to create a structured implementation plan outlining the necessary tasks, required resources, assigned responsibilities, and defined timelines.
A critical part of this stage is scheduling. Changes should be implemented at a time that minimizes disruption to users and business operations, often during maintenance windows or off-peak hours.
Proper planning ensures that the change is introduced in a controlled manner and that contingency or rollback measures are ready if needed.
A Final Perspective
In IT operations, where even small configuration changes can have widespread consequences, change management discipline is not optional. It is essential. Infrastructure evolves, security threats emerge, business requirements shift, and technologies become obsolete. Every update, upgrade, replacement, or configuration adjustment introduces a degree of risk. The question is never whether change will happen. The real question is how well it is managed.
Frequently Asked Questions about IT Change Management
1. Why is Change Management important in IT operations?
Change Management reduces the risk of service disruptions when modifications are made to IT systems. Since many outages are caused by poorly controlled changes, a structured process ensures that updates, upgrades, and fixes are assessed, approved, and implemented in a controlled manner. It protects service stability while still enabling improvement and innovation.
3. What are the different types of changes in ITIL?
ITIL categorizes changes into three types:
- Standard changes – Low-risk, routine, and pre-approved.
- Normal changes – Planned changes that require review and approval.
- Emergency changes – Urgent changes needed to resolve incidents or security threats.
This classification allows organizations to apply governance proportionate to risk rather than using a one-size-fits-all approach.
3. What role does IT Asset Management play in Change Management?
IT Asset Management (ITAM) provides the visibility needed to assess change impact accurately. During risk assessment, teams rely on asset data to understand which systems are affected, what dependencies exist, whether hardware is under warranty, and whether software licensing or compliance requirements are involved. Without accurate asset information, change decisions are made with incomplete context.
4. Is it necessary to integrate IT asset tracking and Change Management?
When ITAM and Change Management are integrated:
- Change requests automatically reference verified asset records
- Risk assessments pull real-time dependency and lifecycle data
- Approvals consider licensing and compliance exposure
- Asset databases are updated automatically after implementation
5. Can Change Management be automated?
Yes, especially for low-risk, repeatable changes. Standard changes are strong candidates for automation because they follow predefined and approved procedures. However, higher-risk changes still require human evaluation and authorization.